Quantum computing is no longer science fiction—it’s reshaping cybersecurity today, and quantum signature algorithms are leading this revolutionary transformation in digital authentication and data protection.
🔐 The Dawn of Quantum Cryptography
As we stand at the precipice of a technological revolution, quantum computing threatens to unravel the cryptographic foundations that secure our digital world. Traditional signature algorithms like RSA and ECDSA, which have protected our communications for decades, face an existential threat from quantum computers powerful enough to break them within hours or even minutes. This looming crisis has sparked an urgent race to develop quantum-resistant signature schemes capable of withstanding attacks from both classical and quantum adversaries.
Quantum signature algorithms represent a fundamental shift in how we approach digital security. Unlike their classical predecessors, these advanced cryptographic systems leverage mathematical problems that remain computationally infeasible even for quantum computers. The transition to quantum-safe signatures isn’t merely an upgrade—it’s a necessary evolution to preserve the integrity of digital communications, financial transactions, software updates, and countless other operations that depend on cryptographic authentication.
The urgency of this transition cannot be overstated. Security experts warn about “harvest now, decrypt later” attacks, where adversaries collect encrypted data today with the intention of decrypting it once quantum computers become sufficiently powerful. Organizations that fail to prepare for the quantum threat risk exposing sensitive information retroactively, making the implementation of quantum signature algorithms a critical priority for forward-thinking enterprises.
Understanding the Quantum Threat Landscape
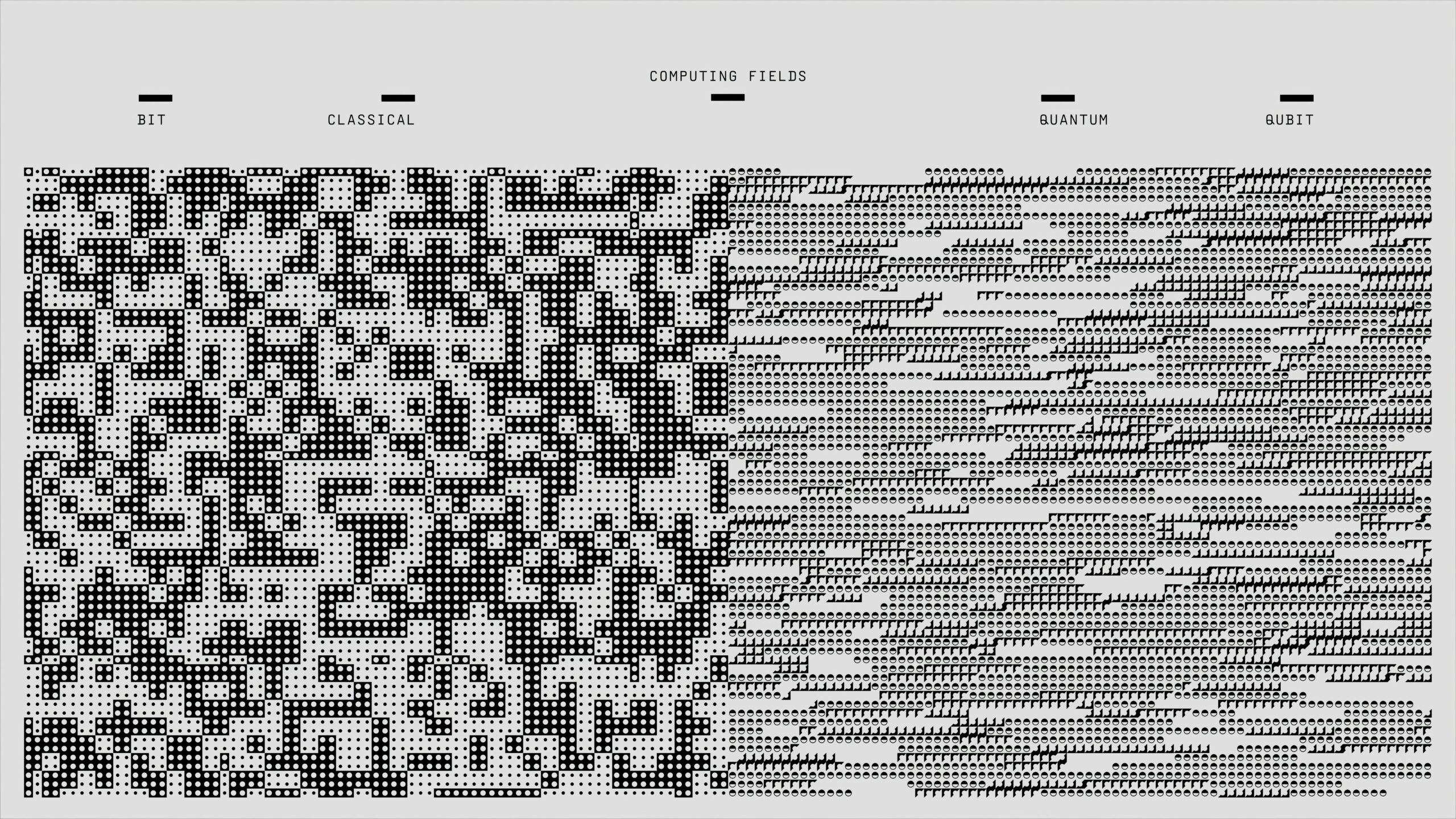
To appreciate the revolutionary nature of quantum signature algorithms, we must first understand the vulnerability of current cryptographic systems. Classical digital signatures rely on mathematical problems like integer factorization and discrete logarithms—problems that are computationally difficult for traditional computers but trivial for sufficiently advanced quantum computers using Shor’s algorithm.
When a quantum computer with enough qubits becomes operational, it could theoretically break RSA-2048 encryption in a matter of hours. This capability would compromise virtually all secure communications, digital signatures, and authentication systems currently in use. The implications extend far beyond individual privacy concerns—critical infrastructure, national security systems, financial networks, and healthcare databases would all be at risk.
The timeline for this quantum threat remains uncertain, but experts estimate that quantum computers capable of breaking current encryption could emerge within 10-20 years. However, the cryptographic community operates under the principle that organizations need to begin transitioning now, as the process of updating cryptographic infrastructure across global systems will take years to complete safely and thoroughly.
🚀 Core Principles of Quantum Signature Algorithms
Quantum signature algorithms, also known as post-quantum signature schemes, are built on mathematical problems that resist both classical and quantum attacks. These algorithms don’t require quantum computers to operate—they run efficiently on conventional hardware while providing security against quantum threats. This characteristic makes them practical for immediate deployment while offering future-proof protection.
The foundational security of these algorithms rests on several hard mathematical problems. Hash-based signatures rely on the security of cryptographic hash functions, lattice-based signatures depend on the difficulty of lattice problems like Learning With Errors (LWE), and multivariate signatures are grounded in the complexity of solving systems of multivariate polynomial equations. Code-based signatures leverage the difficulty of decoding random linear codes, while isogeny-based signatures utilize the computational complexity of finding isogenies between elliptic curves.
Each approach offers distinct advantages and trade-offs in terms of signature size, signing speed, verification time, and key sizes. Organizations must carefully evaluate these factors based on their specific use cases and performance requirements when selecting quantum signature algorithms for implementation.
Leading Quantum Signature Algorithm Families
The National Institute of Standards and Technology (NIST) has been spearheading efforts to standardize post-quantum cryptographic algorithms since 2016. After rigorous evaluation of numerous candidates, NIST selected several quantum signature algorithms for standardization, each representing different cryptographic approaches and offering unique benefits.
CRYSTALS-Dilithium: The Lattice-Based Champion 💎
CRYSTALS-Dilithium emerged as NIST’s primary recommended algorithm for general-purpose digital signatures. This lattice-based signature scheme offers an excellent balance of security, efficiency, and practicality. Dilithium generates relatively compact signatures and operates with impressive speed on modern processors, making it suitable for widespread deployment across diverse applications.
The algorithm’s security foundation rests on the hardness of lattice problems, specifically the Module Learning With Errors (MLWE) problem. This mathematical basis has withstood extensive cryptanalysis and shows no vulnerability to known quantum attacks. Dilithium supports multiple security levels, allowing organizations to choose appropriate parameters based on their security requirements and performance constraints.
Implementation studies demonstrate that Dilithium performs admirably in real-world scenarios, from securing web communications to authenticating software updates. Its efficiency makes it particularly attractive for applications requiring high-volume signature generation and verification, such as blockchain systems, certificate authorities, and secure messaging platforms.
FALCON: Speed and Compactness Combined 🦅
FALCON (Fast Fourier Lattice-based Compact Signatures over NTRU) represents another lattice-based approach that prioritizes signature compactness and verification efficiency. FALCON produces significantly smaller signatures than Dilithium, making it ideal for bandwidth-constrained environments and applications where signature size critically impacts performance.
The algorithm’s foundation in NTRU lattices provides strong security guarantees while enabling faster verification compared to many alternatives. This characteristic proves particularly valuable in scenarios where numerous signatures require verification, such as blockchain validation, secure boot processes, and high-frequency trading systems.
However, FALCON’s implementation complexity exceeds that of Dilithium, requiring more sophisticated programming techniques and careful attention to side-channel resistance. Organizations with the technical expertise to implement FALCON correctly can benefit from its superior performance characteristics in specific use cases.
SPHINCS+: The Conservative Choice 🌳
SPHINCS+ takes a fundamentally different approach by basing its security solely on hash functions rather than structured mathematical problems. This conservative design philosophy offers a critical advantage: if researchers discover vulnerabilities in lattice problems or other mathematical structures, hash-based signatures like SPHINCS+ would remain secure as long as the underlying hash functions remain strong.
The algorithm generates stateless signatures, eliminating the state management complexities that plague some other hash-based schemes. This property simplifies implementation and reduces the risk of catastrophic failures due to state compromise or mismanagement.
SPHINCS+ does produce larger signatures than lattice-based alternatives and requires more computational resources for signing operations. These trade-offs make it less suitable for high-volume or bandwidth-constrained applications but ideal for scenarios where maximum security assurance and implementation simplicity take precedence over performance.
🎯 Real-World Implementation Strategies
Transitioning to quantum signature algorithms requires careful planning and phased implementation to minimize disruption while maximizing security. Organizations should begin by conducting comprehensive cryptographic inventories to identify all systems and applications currently using classical signature algorithms. This assessment provides the foundation for developing migration strategies tailored to specific operational requirements.
Hybrid approaches offer an attractive intermediate solution, combining classical and quantum-resistant signatures to maintain backward compatibility while adding quantum protection. These hybrid schemes allow organizations to transition gradually, reducing implementation risks and providing defense-in-depth security that protects against both current and future threats.
Testing and validation represent critical phases of any quantum signature implementation. Organizations must verify that new algorithms perform acceptably within their specific environments, checking compatibility with existing systems, measuring performance impacts, and ensuring that security properties meet requirements. Pilot deployments in non-critical systems provide valuable learning opportunities before full-scale rollouts.
Performance Considerations and Optimization
Quantum signature algorithms generally require more computational resources than classical alternatives, though the performance gap continues to narrow through ongoing optimization efforts. Key generation typically takes longer, signatures occupy more bytes, and verification may consume additional processing time. However, modern hardware acceleration techniques and algorithmic improvements are steadily enhancing performance.
Hardware acceleration through specialized instructions and dedicated cryptographic processors can dramatically improve quantum signature algorithm performance. Recent processor generations include instructions optimized for polynomial multiplication and other operations common in lattice-based cryptography, significantly boosting Dilithium and FALCON performance.
Network bandwidth considerations emerge as important factors when deploying quantum signatures at scale. Larger signature sizes increase transmission overhead, potentially impacting applications sensitive to packet size or bandwidth consumption. Organizations must evaluate these impacts and potentially optimize protocols to accommodate larger cryptographic artifacts efficiently.
🔬 Integration Challenges and Solutions
Integrating quantum signature algorithms into existing infrastructure presents numerous technical challenges. Legacy systems may lack support for new algorithm identifiers, require updates to cryptographic libraries, or need modifications to accommodate larger keys and signatures. Certificate authorities must update their systems to issue quantum-safe certificates, while relying parties need capabilities to validate them.
Protocol updates often prove necessary when transitioning to quantum signatures. TLS, SSH, IPsec, and other security protocols require modifications to negotiate and utilize post-quantum algorithms. Fortunately, standards bodies are actively developing updated protocol specifications that incorporate quantum-resistant cryptography while maintaining backward compatibility where possible.
Interoperability testing ensures that different implementations of quantum signature algorithms work together correctly. Organizations should participate in industry-wide testing events and verify compatibility with partners’ systems before production deployment. These validation efforts identify integration issues early, preventing costly disruptions later.
Regulatory Landscape and Compliance Requirements
Governments and regulatory bodies worldwide are beginning to mandate timelines for quantum-safe cryptography adoption. The United States has established requirements for federal agencies to inventory cryptographic systems and develop migration plans. The European Union is advancing similar initiatives, while financial regulators increasingly scrutinize organizations’ quantum readiness as part of cybersecurity assessments.
Compliance frameworks are evolving to incorporate quantum cryptography requirements. Organizations in regulated industries should monitor guidance from relevant authorities and proactively align their quantum signature implementation strategies with emerging requirements. Early adoption not only ensures compliance but demonstrates security leadership and may provide competitive advantages.
International cooperation on quantum cryptography standards facilitates global interoperability and reduces implementation complexity. NIST’s standardization process has attracted international participation, and other standards bodies are harmonizing their efforts to create consistent global frameworks for quantum-resistant cryptography.
🌐 Industry-Specific Applications and Use Cases
Financial services face particularly acute quantum signature challenges due to the long-term value of financial data and the critical importance of transaction authentication. Banks and payment processors are actively piloting quantum signature implementations for securing transactions, authenticating customers, and protecting sensitive financial communications. The immutability requirements of financial records make quantum-safe signatures essential for preserving long-term data integrity.
Healthcare organizations manage sensitive patient information subject to strict privacy regulations and long retention periods. Quantum signatures enable these organizations to ensure the authenticity and integrity of medical records, secure telemedicine communications, and protect connected medical device data against future quantum threats. The potential for patient harm from compromised medical data makes quantum readiness a patient safety issue.
Government and defense sectors handle classified information requiring protection for decades or longer. Intelligence agencies and military organizations are among the earliest adopters of quantum signature technology, implementing these algorithms to secure classified communications, authenticate command and control systems, and protect national security secrets from quantum-enabled adversaries.
Software development and distribution rely heavily on digital signatures to authenticate updates and verify code integrity. Compromised software signatures could enable widespread malware distribution, making quantum-resistant signatures critical for supply chain security. Major software vendors are integrating quantum signature capabilities into their development and distribution pipelines to future-proof their security infrastructure.
Future Developments and Research Directions
The field of quantum signature algorithms continues evolving rapidly, with researchers exploring new mathematical foundations and optimization techniques. Emerging approaches like isogeny-based signatures offer promising alternatives with unique security properties and compact signature sizes, though they require further analysis before widespread deployment.
Standardization efforts extend beyond NIST’s initial selections, with ongoing evaluations of additional algorithms and specialized use cases. Future standards will likely address specific scenarios like lightweight cryptography for constrained devices, high-security applications requiring maximum assurance, and ultra-high-performance systems demanding minimal overhead.
Quantum computing itself continues advancing, potentially altering the threat landscape. Researchers monitor quantum computing progress closely, ready to adjust security parameters or recommend alternative algorithms if quantum capabilities develop faster than anticipated. This adaptive approach ensures that quantum signature algorithms maintain appropriate security margins against evolving threats.
🎓 Building Organizational Quantum Readiness
Developing organizational quantum readiness requires more than technical implementation—it demands cultural change, skills development, and strategic planning. Leadership must understand the quantum threat and commit resources to addressing it proactively rather than reactively. This commitment includes funding migration projects, supporting staff training, and prioritizing quantum security in strategic technology planning.
Skills development represents a critical investment for organizations transitioning to quantum signatures. Cryptography teams need training on post-quantum algorithms, implementation best practices, and security analysis techniques specific to quantum-resistant schemes. Development teams require education on integrating new cryptographic libraries and updating applications to utilize quantum signatures effectively.
Collaboration and information sharing accelerate quantum readiness across industries. Organizations should participate in industry consortia, attend quantum cryptography conferences, and engage with vendors and researchers advancing the field. These collaborative efforts identify best practices, share lessons learned, and build the collective expertise necessary for successful quantum transitions.
💡 Maximizing Return on Quantum Signature Investment
Organizations investing in quantum signature technology should view the transition as an opportunity to modernize their entire cryptographic infrastructure. Quantum migrations provide natural inflection points for updating aging systems, eliminating technical debt, and implementing more robust security architectures. By coupling quantum implementations with broader security improvements, organizations maximize the value derived from migration investments.
Future-proofing security infrastructure requires cryptographic agility—the ability to update algorithms quickly as threats evolve or vulnerabilities emerge. Implementing abstraction layers that separate cryptographic operations from application logic enables organizations to swap algorithms without extensive code modifications. This architectural approach reduces future migration costs and accelerates response to emerging security challenges.
The transition to quantum signatures positions organizations as security leaders, potentially providing competitive advantages in security-conscious markets. Organizations that complete quantum migrations early can market their quantum-ready security, attract security-focused customers, and differentiate themselves from competitors still using vulnerable classical cryptography.
🚪 Opening New Possibilities Through Quantum Security
As quantum signature algorithms mature and deployment accelerates, they’re unlocking new possibilities for secure digital interactions. The enhanced security properties of post-quantum cryptography enable applications previously considered too risky, extend protection horizons for long-term data preservation, and create foundations for quantum-safe distributed systems that can operate securely in the quantum era.
The convergence of quantum signatures with other emerging technologies creates exciting opportunities. Blockchain systems implementing quantum-resistant signatures gain long-term viability and enhanced security. Internet of Things ecosystems can authenticate devices using compact quantum signatures, preventing compromise even by future quantum attackers. Cloud computing platforms offering quantum-safe cryptography as a service democratize access to advanced security capabilities.
Ultimately, quantum signature algorithms represent more than defensive measures against quantum threats—they’re enablers of a more secure digital future. By harnessing these powerful cryptographic tools today, organizations protect their data tomorrow and position themselves at the forefront of the quantum computing revolution. The future of digital security is quantum-resistant, and that future is arriving now.
Toni Santos is a quantum-systems researcher and forward-thinking writer exploring how quantum biology, entanglement, and emergent realities reshape our understanding of life, energy, and consciousness. Through his investigations into quantum communication, energy systems, and mind-science, Toni examines how the unseen dimensions of reality might inform the shape of our future. Passionate about bridging rigorous science and visionary insight, Toni focuses on how quantum phenomena influence biology, connectivity and human experience. His work highlights the convergence of quantum theory, technological innovation and human awareness — guiding readers toward a deeper understanding of possibility and presence. Blending physics, systems theory and consciousness research, Toni writes about the architecture of reality itself — helping readers understand how space, time and mind intersect in the quantum domain. His work is a tribute to: The hidden quantum patterns behind life and awareness The future of communication through entanglement and connection The vision of reality as dynamic, participatory, and alive Whether you are a scientist, philosopher or open-minded explorer of new realities, Toni Santos invites you to dive into the quantum frontier — one principle, one experiment, one insight at a time.