The digital world stands at a crossroads where quantum computing threatens to shatter today’s encryption methods, making post-quantum cryptography our essential shield.
🔐 Why Tomorrow’s Security Can’t Wait Until Tomorrow
Imagine waking up one morning to discover that every encrypted message, financial transaction, and secure communication from the past decade has been deciphered overnight. This isn’t science fiction—it’s the looming threat that quantum computers pose to our current cryptographic infrastructure. As researchers push quantum computing capabilities forward, the cybersecurity community races to develop unbreakable shields capable of withstanding attacks from machines that don’t yet exist in their full power.
Post-quantum cryptography represents humanity’s preemptive strike against this future vulnerability. Unlike reactive security measures that patch holes after breaches occur, this forward-thinking approach aims to fortify our digital fortresses before quantum adversaries can storm the gates. The stakes couldn’t be higher: government secrets, intellectual property, healthcare records, financial systems, and personal privacy all hang in the balance.
The Quantum Threat: Understanding What We’re Up Against
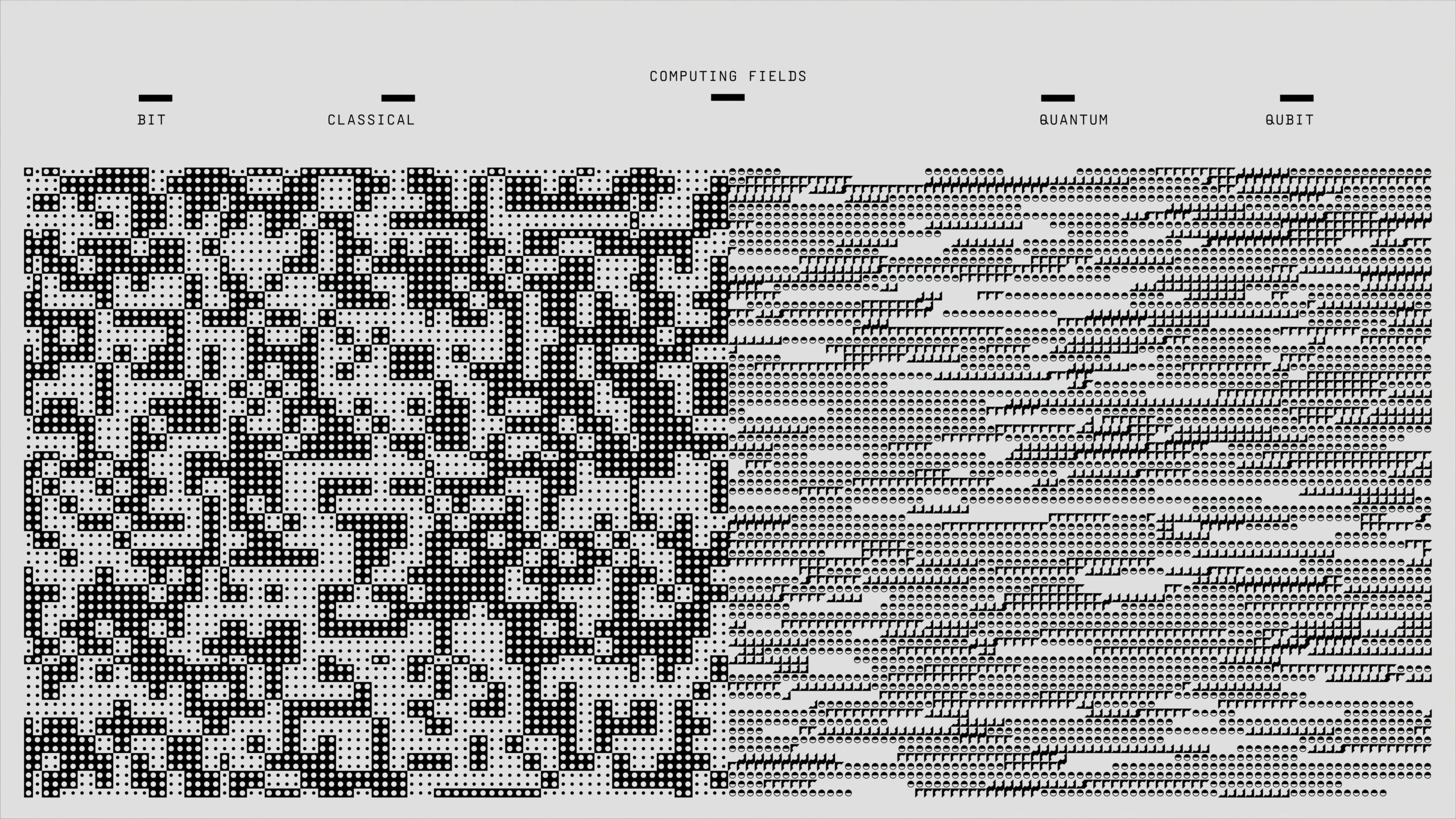
Traditional encryption methods like RSA and elliptic curve cryptography have served us well for decades. They rely on mathematical problems that classical computers find extraordinarily difficult to solve—factoring large numbers or solving discrete logarithm problems. A conventional computer would need thousands of years to crack properly implemented RSA-2048 encryption.
Quantum computers, however, play by entirely different rules. Leveraging quantum mechanical phenomena like superposition and entanglement, these machines can explore multiple solution pathways simultaneously. Shor’s algorithm, developed in 1994, demonstrated that a sufficiently powerful quantum computer could factor large numbers exponentially faster than classical computers, effectively rendering RSA and similar algorithms obsolete.
The Harvest Now, Decrypt Later Strategy 🎯
Perhaps even more concerning than future quantum attacks is what security experts call “harvest now, decrypt later.” Adversaries are already collecting encrypted data today, storing it with the intention of decrypting it once quantum computers become powerful enough. This means that sensitive information encrypted today but valuable for years to come—medical records, state secrets, long-term business strategies—is already compromised, just waiting for technology to catch up.
This reality compresses our timeline dramatically. We cannot wait until quantum computers achieve full maturity. The transition to quantum-resistant algorithms must happen now, while our current encryption still holds.
Building Tomorrow’s Cryptographic Foundations Today
Post-quantum cryptography doesn’t involve quantum mechanics itself—a common misconception. Instead, it comprises mathematical algorithms that remain secure even when attacked by quantum computers. These algorithms fall into several distinct families, each with unique advantages and trade-offs.
Lattice-Based Cryptography: The Rising Star
Lattice-based schemes have emerged as frontrunners in the post-quantum race. These systems base their security on the difficulty of finding the shortest or closest vector in a high-dimensional lattice—a problem that remains hard even for quantum computers. CRYSTALS-Kyber and CRYSTALS-Dilithium, both lattice-based algorithms, were selected by NIST as primary standards for post-quantum key encapsulation and digital signatures respectively.
The appeal of lattice-based cryptography extends beyond quantum resistance. These schemes offer efficiency in both computation and key size, making them practical for real-world deployment. They also enable advanced cryptographic primitives like fully homomorphic encryption, which allows computations on encrypted data without decrypting it first.
Hash-Based Signatures: Time-Tested Security
Hash-based signature schemes represent the conservative choice in post-quantum cryptography. Their security relies solely on the cryptographic properties of hash functions, which are well-understood and have withstood decades of cryptanalysis. SPHINCS+, selected by NIST as a standard, exemplifies this approach.
The primary drawback of hash-based signatures involves size—both signature sizes and key sizes tend to be larger than other post-quantum alternatives. However, their proven security foundation makes them attractive for applications where absolute confidence outweighs efficiency concerns.
Code-Based Cryptography: The Veteran Approach
Code-based cryptography traces its roots back to 1978 with Robert McEliece’s original cryptosystem. These schemes base their security on the difficulty of decoding general linear codes, a problem that has resisted both classical and quantum attacks for over four decades. Classic McEliece received NIST selection as an alternative standard for key encapsulation.
While code-based systems offer strong security guarantees and fast encryption/decryption, they suffer from extremely large public key sizes—sometimes several hundred kilobytes or even megabytes. This makes them less suitable for bandwidth-constrained environments but perfectly viable for applications where key size isn’t critical.
Isogeny-Based and Multivariate Cryptography 🔬
Other mathematical approaches round out the post-quantum toolkit. Isogeny-based cryptography, which relies on the difficulty of finding paths between elliptic curves, offers remarkably small key sizes but has faced recent cryptanalytic advances that have eliminated some candidates. Multivariate cryptography, based on the difficulty of solving systems of multivariate polynomial equations, continues to evolve with new proposals emerging regularly.
The NIST Standardization Journey: Setting Global Benchmarks
The National Institute of Standards and Technology (NIST) launched its post-quantum cryptography standardization process in 2016, inviting researchers worldwide to submit candidate algorithms. This open, transparent competition mirrors the successful process that selected AES as the Advanced Encryption Standard decades earlier.
After multiple rounds of evaluation, testing, and cryptanalysis, NIST announced its first selections in July 2022:
- CRYSTALS-Kyber: Primary standard for general encryption and key establishment
- CRYSTALS-Dilithium: Primary standard for digital signatures
- FALCON: Alternative signature standard optimized for applications needing smaller signatures
- SPHINCS+: Alternative signature standard based on hash functions
Additional candidates remain under consideration for future standardization, recognizing that cryptographic diversity provides resilience against unexpected breakthroughs that might compromise any single algorithm family.
Implementation Timelines and Real-World Adoption
NIST’s draft standards, published in 2023, provide concrete specifications for implementers. However, standardization represents just the beginning. The real challenge lies in deploying these algorithms across the vast landscape of existing systems, protocols, and applications.
Major technology companies have already begun integration efforts. Google has experimented with post-quantum key exchange in Chrome. Cloudflare and AWS offer post-quantum TLS options for customers wanting to test these waters. Apple announced post-quantum encryption for iMessage, demonstrating commitment at the consumer application level.
Practical Challenges in the Quantum Transition 💼
Transitioning to post-quantum cryptography isn’t simply a matter of swapping out one algorithm for another. The process involves navigating numerous technical, operational, and strategic challenges.
Performance and Resource Considerations
Post-quantum algorithms generally require more computational resources than their classical counterparts. Signature sizes might be larger, key generation slower, or verification more processing-intensive. For resource-constrained devices—IoT sensors, smart cards, embedded systems—these differences matter significantly.
Organizations must carefully evaluate performance impacts across their entire technology stack. What runs seamlessly on modern servers might strain older hardware or mobile devices. Performance testing under realistic conditions becomes crucial before committing to full-scale deployment.
Hybrid Approaches: Bridging Two Cryptographic Eras
Many experts recommend hybrid cryptographic schemes that combine classical and post-quantum algorithms. A hybrid approach might use both RSA and CRYSTALS-Kyber together, providing security if either algorithm proves vulnerable while adding only modest overhead.
This strategy offers insurance against two scenarios: the possibility that quantum computers arrive sooner than expected (protecting against attacks on classical algorithms) and the risk that newly standardized post-quantum algorithms contain undiscovered weaknesses (maintaining protection through classical algorithms until post-quantum schemes prove themselves further).
Protocol and Infrastructure Updates
Cryptographic algorithms don’t exist in isolation—they’re embedded within protocols like TLS, SSH, IPsec, and countless others. Each protocol requires updates to accommodate post-quantum algorithms, which may involve new message formats, negotiation mechanisms, and compatibility considerations.
Certificate authorities must prepare to issue post-quantum certificates. Key management systems need updates to handle new key types and sizes. Hardware security modules require firmware updates supporting new algorithms. The interconnected nature of cryptographic infrastructure means changes ripple through entire systems.
Industry-Specific Implementation Roadmaps 🗺️
Different sectors face unique challenges and timelines in their quantum transition journeys.
Financial Services: Where Time Equals Money
Banks and financial institutions handle transactions requiring both immediate security and long-term confidentiality. Payment systems, trading platforms, and banking infrastructure represent high-value targets for adversaries willing to harvest encrypted data for future decryption.
Regulatory frameworks increasingly recognize quantum threats. Financial regulators are beginning to require quantum-risk assessments and transition planning. Major banks have established quantum working groups, conducting cryptographic inventories to identify which systems require prioritized updates.
Healthcare: Protecting Lifetime Privacy
Medical records demand protection spanning decades—genetic information remains relevant throughout a patient’s lifetime. Healthcare providers must ensure that patient data encrypted today remains confidential fifty years from now.
The healthcare sector faces additional complications from legacy systems and medical devices with long operational lifespans. A hospital MRI machine might operate for fifteen years, yet its cryptographic components need quantum-resistant updates far sooner.
Government and Defense: National Security Stakes
Government agencies handle classified information with sensitivity periods extending decades into the future. Defense departments recognize that today’s encrypted military communications could compromise national security if decrypted in 2040.
Many government organizations have already mandated post-quantum transitions. The NSA’s Commercial National Security Algorithm Suite 2.0 specifies quantum-resistant algorithms for protecting national security systems, signaling clear direction for contractors and partners.
The Developer’s Perspective: Building Quantum-Safe Applications 👨💻
Software developers play crucial roles in the post-quantum transition. Writing quantum-safe code requires understanding not just which algorithms to use but how to use them correctly.
Cryptographic Agility: Future-Proofing Your Code
Smart developers embrace cryptographic agility—designing systems that can swap cryptographic algorithms without requiring complete rewrites. Rather than hardcoding specific algorithms, agile systems abstract cryptographic operations behind interfaces that enable algorithm updates as standards evolve.
This approach protects against two scenarios: needing to update when quantum computers arrive and needing to switch if vulnerabilities emerge in chosen post-quantum algorithms. Agility turns cryptographic updates from architectural nightmares into manageable configuration changes.
Testing and Validation Frameworks
Robust testing becomes paramount when implementing post-quantum algorithms. Test vectors provided by NIST help verify correct implementation, but real-world testing must go further. Side-channel resistance, performance under load, interoperability with other implementations—all require thorough validation.
Open-source libraries like liboqs (Open Quantum Safe project) provide reference implementations facilitating experimentation and integration. These resources accelerate development while promoting consistent, vetted implementations rather than custom code prone to subtle security flaws.
Looking Beyond Standards: Emerging Frontiers in Quantum-Safe Security 🚀
While current standardization efforts focus on replacing vulnerable algorithms, researchers continue exploring new frontiers in post-quantum cryptography.
Zero-Knowledge Proofs in a Quantum World
Zero-knowledge proofs allow one party to prove knowledge of information without revealing the information itself. These powerful primitives enable privacy-preserving authentication and verification. Researchers actively develop quantum-resistant zero-knowledge systems, ensuring these privacy-enhancing technologies survive the quantum transition.
Quantum Key Distribution: A Complementary Approach
Quantum key distribution (QKD) uses quantum mechanical principles to detect eavesdropping on key exchange. Unlike post-quantum cryptography, QKD requires specialized hardware and dedicated fiber optic connections, limiting its applicability to specific high-security scenarios.
Rather than competing with post-quantum cryptography, QKD serves complementary roles. Government facilities and financial institutions might use QKD for key distribution between fixed sites while employing post-quantum algorithms for general encryption and authentication across broader networks.
Homomorphic Encryption: Computing on Encrypted Data
Fully homomorphic encryption enables arbitrary computations on encrypted data without decryption. This technology promises revolutionary privacy protections—cloud providers could process your data without ever accessing it in plaintext. Lattice-based post-quantum schemes naturally support homomorphic properties, creating synergies between quantum resistance and advanced functionality.
Preparing Your Organization: A Strategic Action Plan 📋
Organizations shouldn’t wait for quantum computers to arrive before beginning their transition. Strategic preparation today prevents crisis-driven scrambles tomorrow.
Conducting Cryptographic Inventories
Understanding what needs protection represents the crucial first step. Comprehensive cryptographic inventories catalog all systems using cryptography: applications, protocols, hardware components, third-party services, and data stores. This inventory identifies which assets face quantum threats and helps prioritize remediation efforts.
Risk Assessment and Prioritization
Not all systems require immediate updates. Risk-based prioritization considers data sensitivity, expected system lifespan, and threat timelines. Systems handling highly sensitive data with long confidentiality requirements demand earlier transitions than applications processing ephemeral information.
Vendor Engagement and Supply Chain Security
Modern organizations rely on countless third-party vendors, each potentially introducing cryptographic dependencies. Engaging vendors about their quantum transition plans, requesting roadmaps, and incorporating post-quantum requirements into procurement processes ensures your supply chain doesn’t become your weakest link.
The Race Against Time: Why Urgency Matters ⏰
Some observers ask whether the quantum threat deserves such urgent attention when large-scale quantum computers remain years away. Multiple factors justify immediate action.
First, the harvest-now-decrypt-later threat means delays in transitioning expose today’s data to tomorrow’s attacks. Second, large-scale cryptographic transitions historically take far longer than anticipated—organizations underestimate the complexity and interconnectedness of their cryptographic dependencies. Third, waiting until quantum computers arrive guarantees transition happens under crisis conditions, increasing errors and vulnerabilities.
The most compelling argument for urgency comes from history. When researchers discovered practical attacks against MD5 and SHA-1 hash functions, many assumed transitions would happen quickly. Yet years later, vulnerable systems remained widespread despite known risks. Cryptographic inertia is real, making early starts essential.
Collaborative Defense: Global Cooperation in Quantum Preparedness 🌍
The quantum threat knows no borders. International cooperation accelerates progress through shared research, coordinated standards, and collective security.
Organizations like ETSI (European Telecommunications Standards Institute), ISO/IEC, and ITU contribute to harmonizing post-quantum standards globally. Academic researchers collaborate across continents, conducting cryptanalysis that strengthens confidence in proposed algorithms. Open-source projects pool expertise from worldwide contributors.
This collaborative spirit reflects an understanding that quantum threats affect everyone. A vulnerability discovered by researchers in one country protects users everywhere. Standardization efforts incorporating diverse perspectives produce stronger, more thoroughly vetted solutions.
Beyond Cryptography: Quantum-Safe Thinking 🧠
While post-quantum cryptography addresses specific algorithmic vulnerabilities, truly quantum-safe security requires broader thinking. Security architectures must assume cryptographic algorithms have finite lifespans. Defense-in-depth strategies that don’t rely solely on cryptographic protection become even more valuable.
Organizations should cultivate cultures of cryptographic awareness where developers, architects, and decision-makers understand that today’s secure algorithms become tomorrow’s vulnerabilities. This mindset encourages ongoing vigilance, regular reassessment, and willingness to adapt as the threat landscape evolves.
The Path Forward: Building Truly Unbreakable Shields
Post-quantum cryptography represents humanity’s best current defense against quantum computing threats. The algorithms selected through rigorous cryptanalysis, the standards emerging from transparent international processes, and the implementation efforts underway across industries collectively form shields designed to remain unbreakable even against adversaries wielding quantum computers.
Yet the journey continues. Cryptography never stops evolving. Ongoing research explores new mathematical foundations, discovers optimizations, and occasionally uncovers vulnerabilities requiring adjustments. The cryptographic community maintains vigilance, ready to respond as our understanding deepens and technology advances.
The quantum transition challenges us to think decades ahead, protecting today’s data against tomorrow’s threats. Success requires technical excellence, strategic planning, international cooperation, and sustained commitment. Organizations beginning their quantum journey today position themselves as leaders in the secure digital future, while those delaying face growing risks and eventual crisis-driven transitions.
As quantum computers progress from laboratory curiosities to practical reality, our post-quantum cryptographic shields must already be in place, tested, and proven. The future of digital security depends on actions taken today. The shields we forge now must prove truly unbreakable—our privacy, security, and trust in digital systems demand nothing less.
Toni Santos is a quantum-systems researcher and forward-thinking writer exploring how quantum biology, entanglement, and emergent realities reshape our understanding of life, energy, and consciousness. Through his investigations into quantum communication, energy systems, and mind-science, Toni examines how the unseen dimensions of reality might inform the shape of our future. Passionate about bridging rigorous science and visionary insight, Toni focuses on how quantum phenomena influence biology, connectivity and human experience. His work highlights the convergence of quantum theory, technological innovation and human awareness — guiding readers toward a deeper understanding of possibility and presence. Blending physics, systems theory and consciousness research, Toni writes about the architecture of reality itself — helping readers understand how space, time and mind intersect in the quantum domain. His work is a tribute to: The hidden quantum patterns behind life and awareness The future of communication through entanglement and connection The vision of reality as dynamic, participatory, and alive Whether you are a scientist, philosopher or open-minded explorer of new realities, Toni Santos invites you to dive into the quantum frontier — one principle, one experiment, one insight at a time.